Controlling Duplicate Payments with Automation and Process Design
Introduction
Even with the advanced ERP systems that most large companies utilize for Accounts Payable processing, the challenge of duplicate payments and fraud control, in general, continues to be an issue for many AP organizations. Considering the tremendous number of invoices being processed and the corresponding amount of supplier payments being made at most companies, even a duplicate payment percentage of significantly less than 1% can still result in millions of dollars of exposure to loss for the company, regardless of whether it is a consequence of deliberate fraud, a system weakness, or a lack of adequate process design or controls.
Company Experiences
A recent Peercast discussion in Peeriosity’s Accounts Payable (P2P) research area featured a global company with $20B in annual revenue discussing its approach to identifying and preventing duplicate payments. The top reasons for duplicate payments identified included manual keying errors, duplicate supplier records, multiple payments or invoicing platforms, ineffective system controls, and poor process controls.
Key initiatives to address the duplicate payment issue included:
- Process controls and user training to a standardized process are followed for entering information, including invoice number formatting, the date field, the amount, and how to select the payment to the vendor
- The system controls in place to capture at the entry stage based on invoice number and date
- Creating a duplicate payment check automation tool to use in combination with the implementation of Talia as a supplier portal
- Cleaning up the vendor master file and deactivating duplicate vendor records
- 100% review of PO invoices over $20,000, and all check requests and one-time payments
- Vendor statement and duplicate payment audit by a 3rd party recovery firm
- Currently testing artificial intelligence solutions to identify duplicates
Some lessons learned include:
- Standardize data entry to ensure correct data is entered
- Only pay from original invoices
- Clean the vendor file every year
- Use a fixed invoicing method and require suppliers to send invoices by one process only
- Have controls on rush payments and ensure proper backup and approvals before processing
- Limit non-PO invoices to $5K and route invoices using workflow for approval
For details, Peeriosity members are encouraged to sign into the members’ area to view the complete presentation and listen to the recorded Peercast.
iPolling Results Review
Peeriosity’s iPolling was used to provide insight into the effectiveness of processes and systems that Peeriosity member companies use for Accounts Payable duplicate payment detection and control.
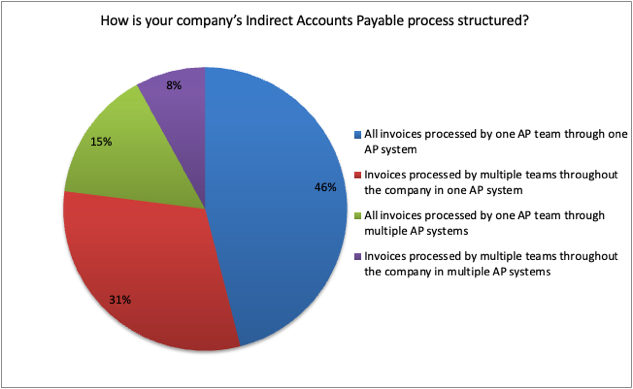
Regarding the structure of Peeriosity member companies’ process for indirect payments, 77% have invoices processed through one AP system, with 46% having invoices processed in one AP system by one AP team, and 31% having invoices processed in one AP system by multiple teams. The remaining 23% have invoices processed using multiple AP systems, with 15% using one team and 8% using multiple teams. Obviously, having robust process controls is easier to implement with a single centralized AP team, with more advanced system controls necessary when more than one AP system is used for processing.
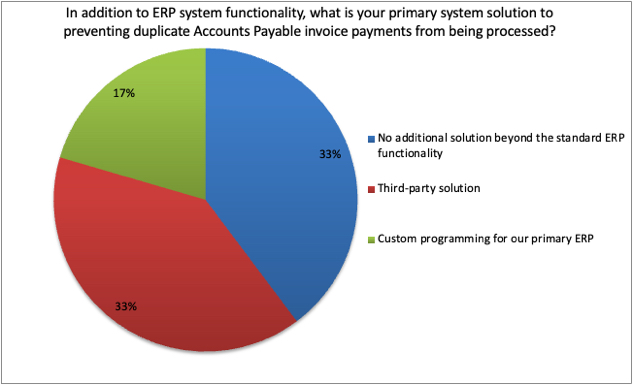
With regards to the primary systems solution used, in addition to duplicate payment control functionality that is pre-packaged into an ERP system, 33% indicate that no additional systems solutions are used, 33% use a third-party solution, and 17% have completed customized programming for their primary ERP. Not having a complete systems solution means companies are relying primarily on after-the-fact reviews by internal resources or duplicate payments recovery firms to identify and recover duplicate payments, which can be an expensive and risky approach to managing and controlling duplicates.
A few of the comments from members include:
- Although we mainly rely on our ERP controls to catch duplicates, we periodically engage with a 3rd party for AP Recovery Audits.
- We had a third-party system check for duplicate payments and we are now transitioning to a new service provider to check duplicate invoices and duplicate payments using their custom-developed tool. We also have standard SAP checks that look for duplicate invoices.
- We rely on ERP controls to catch duplicates, as well as our invoice workflow tool (Tungsten), and perform a 3rd party recovery audit.
- Invoices are processed by various teams located in different regions but all of them report to GBS. There is a single ERP which is SAP and it helps to prevent duplicate documents but not 100%. Besides the ERP system in Mexico Region, there is a third-party solution called Detecno; this system ensures compliance with fiscal government regulations and this solution also prevents 100% of duplicated invoices using an encrypted unique file called CFDI; this solution has communication with the ERP system.
Closing Summary
Having robust processes and systems in place to identify and eliminate duplicate payments is critical, with a significant return on your investment likely. Making the investment up front to prevent duplicate payments is more effective and less costly than relying on duplicate payment recovery firms who may miss duplicates in their review, and who take a percentage of recoveries as part of their fee structure. This is particularly true for Peeriosity member companies with billions of dollars of annual revenue, and billions of annual spending that will include many millions of dollars of indirect purchases where duplicate payments are most likely to occur. Upfront processes and system controls can dramatically reduce the risk of duplicate payments, with a total cost that is significantly less than after-the-fact controls and reviews by recovery firms who charge large fees for recovery.
What level of duplicate payments is your company currently experiencing? Is it time to allocate more resources to this important control issue?
Who are your peers and how are you collaborating with them?
________________________________________________________________________
“Peercasts” are private, professionally facilitated webcasts that feature leading member company experiences on specific topics as a catalyst for broader discussion. Access is available exclusively to Peeriosity member company employees, with consultants or vendors prohibited from attending or accessing discussion content. Members can see who is registered to attend in advance, with discussion recordings, supporting polls, and presentation materials online and available whenever convenient for the member. Using Peeriosity’s integrated email system, Peer Mail, attendees can easily communicate at any time with other attending peers by selecting them from the list of registered attendees.
“iPolling” is available exclusively to Peeriosity member company employees, with consultants or vendors prohibited from participating or accessing content. Members have full visibility of all respondents and their comments. Using Peeriosity’s integrated email system, Peer Mail, members can easily communicate at any time with others who participated in iPolling.
Peeriosity members are invited to log into www.peeriosity.com to join the discussion and connect with Peers. Membership is for practitioners only, with no consultants or vendors permitted. To learn more about Peeriosity, click here.

